Welcome, Crypto Dummies!
If you’re new here, this substack focuses on educating those that know nothing about crypto and blockchain technology.
If that’s you, you’re in the right place!
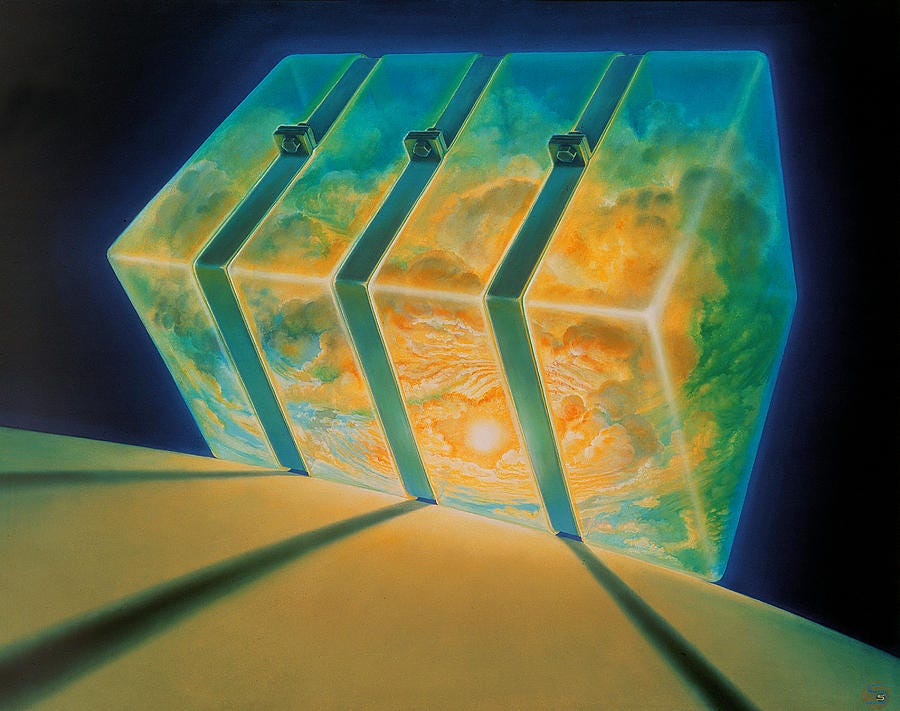
Today we’re going to go over the protocol that aims to be the TCP/IP of Web3 node infrastructure…
The Pocket Network.
What is the Pocket network?
Pocket Network is a decentralized RPC protocol for any blockchain. For those that don’t know, RPC is essentially computer-to-computer service requests.
This helps guide the connection between communicating computers. Pocket is a blockchain relay network for decentralized infrastructure, facilitating dApps and users with Web3 access.
Current blockchains pay for data to be stored on the blockchain and for security, however, they don’t pay for the history, access to the history, or infrastructure of the history of the blockchain.
Pocket Network offers full-node service, meaning users can be incentivized to run the infrastructure of popular blockchains. Full-node operators are paid whenever a relay is routed through their nodes. Pocket Network creates a marketplace to connect applications to web3 and infrastructure providers running full nodes.
Pocket Network solves a critical flaw in the web3 stack. RPC nodes have grown more expensive to maintain and developers more specialized. As a result, Web3 RPC access has consolidated around centralized gatekeepers. Signing transactions in your favorite NFT marketplace or Web3 game, your data flows through a centralized cluster of RPC nodes, leaving you vulnerable to outages.
Pocket Network solves this by incentivizing a network of RPC nodes to relay user data to any blockchain. Decentralized Applications send their RPC requests to nodes who relay the requests using Zero-Knowledge Range Proofs to validate the Relay Evidence that will in turn determine their POKT block rewards.
How does Pocket work?
Pocket consists of 3 key components:
Applications
Nodes
The Network layer
Applications submit relays/API requests that are meant to be routed to any public database node.
Nodes service these relays, submitting them to the public databases they are meant for and returning a response to the application (if necessary).
The Network layer is made up of all the rules, protocols, and finality storage. This serves as the backbone of all interactions between applications and nodes.
Pocket network utilizes ‘Sessions’ as a mechanism to regulate interactions between applications and nodes. These sessions are a data structure, generated following the established Session Generation Algorithm. This uses data from the finality storage layer and pseudo-randomly groups one application with a set of nodes to provide service for a limited period of time.
The Servicing Layer
The Pocket Network’s Servicing layer is made up of 2 main actors:
Applications
Servicers
An Application submits a Relay/API Request to be routed to any Relay Chain. A Servicer ‘services’ the application, routing the Relay Request to the Relay Chain and forwarding the response to the Application. The interaction between Application and Servicer is the fundamental utility of Pocket Network.
Basic Lifecycle
An application must stake the native cryptocurrency $POKT in the network, to register for decentralized infrastructure
The amount of sanctioned throughput (per request) is determined by the amount staked by the application in the network.
Servicers must stake the native cryptocurrency $POKT, to register to provide decentralized infrastructure.
An application is paired with a Servicer, during this time the servicing interaction takes place
Servicer receives an amount of $POKT, proportional to the amount of throughput(requests), for providing the decentralized infrastructure.
Once an Application/Servicer unstakes, they are unregistered from Pocket Network. Their stake is returned to their account.
Application & Validator Security
Application Authentication Tokens are the key mechanism for Applications to balance the security of their stake and the UX of clients during servicing. Using the AAT, an application can sanction clients to access their throughput via a Digital Signature.
Pocket Network encourages Client-Side Validation, sending the same request to multiple validators. These configurations ensure the highest level of data accuracy and enable the Pocket network to use the Application Challange Mechanism, where the corresponding validators providing invalid data are economically penalized.
Pocket network requires both developers and nodes to stake the native cryptocurrency of the network, $POKT, in order to participate in the network. Nodes are incentivized with rewards for fulfilling API requests to developers on a per request basis.
Pocket Network aims to be the TCP/IP of Web3 Infrastructure. The native currency POKT is not meant to be a transactional cryptocurrency, but one to be used to connect Applications to decentralized Web3 node infrastructure. A majority of Layer 1 chains rely predominantly on transaction fees, whereas pocket aims to be a simple fee market with the demand side (applications) burning POKT and the supply side (Service Nodes) receiving newly minted POKT via block rewards. Applications and service nodes must stake POKT to access or provide work to the Pocket network.
The Pocket Network aims to solve the RPC flaw in web3 infrastructure. By introducing the decentralization of RPC nodes, smaller players can play a big role to support the Web3 infrastructure. Centralized Node-as-a-Service companies can lower the barrier for developers to release applications, Pocket network serves to fill the void and bring decentralization to the RPC infrastructure of Web3.
That’s it for today’s post crypto dummies! Hope you enjoyed this post, and tune in next week for more!
Disclaimer: All information in this post is for educational purposes only. None of the information provided is deemed to be investment or financial advice.




Holy crap this is awesome. Had no idea it existed. I know censorship has been a big worry with some providers, as some of them banned certain regions from using their service.